and the distribution of digital products.
DM Television
How Merkle Trees Enhance Data Integrity in Crypto Custody
:::info Authors:
(1) Hamid Bateni, Nobitex Labs ([email protected]);
(2) Keyvan Kambakhsh, Nobitex Labs ([email protected]).
:::
Table of Links2 Proof of Liability and 2.1 Commitment
2.2 Merkle TreeA Merkle Tree is a tree in computer science in which every leaf node is labeled with the cryptographic hash of a data block, and each nonleaf node is labeled with the cryptographic hash of the labels of its child nodes. The value of a non-leaf node is determined by the hash of its children nodes, and this continues recursively until the tree’s root is achieved.
\ This structure is particularly effective because it allows for efficient and secure verification of the contents of large data structures. The Merkle Tree allows us to verify data with a significantly smaller subset of the total information.[7]
\
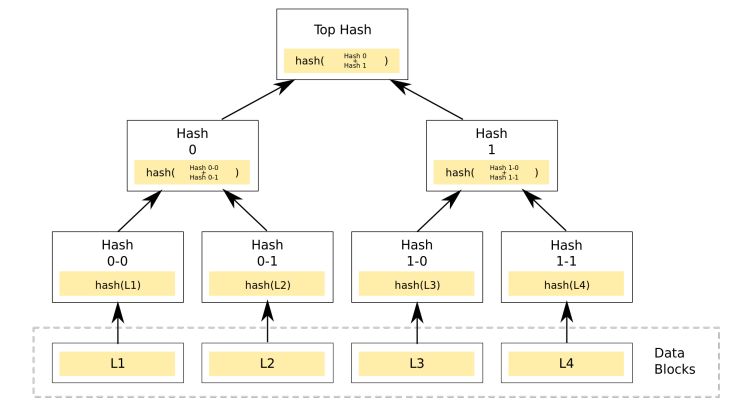
\ In the scenario of Proof of Solvency, we use the Merkle Tree as our cryptographic commitment. The root of the Merkle Tree acts as a commitment to all liabilities, and each leaf in the tree corresponds to a liability. This allows for an efficient and secure way to prove the existence and integrity of liabilities.
\ By using a Merkle Tree, we can provide a proof path for any given leaf node (liability) up to the root. This path, also known as the Merkle path, allows anyone to verify that a specific liability is part of the tree. They can do this by recomputing the hashes from the leaf up to the root and comparing it with the root hash. This approach is particularly useful because it allows for verification without needing access to all data points, providing a balance between transparency and data efficiency.
\ In the following sections, we will delve deeper into the leaf structure of the Merkle Tree and how we can use it to create proof statements.
\
:::info This paper is available on arxiv under CC BY-NC-ND 4.0 DEED license.
:::
\
- Home
- About Us
- Write For Us / Submit Content
- Advertising And Affiliates
- Feeds And Syndication
- Contact Us
- Login
- Privacy
All Rights Reserved. Copyright , Central Coast Communications, Inc.