and the distribution of digital products.
DM Television
How Lending Pools and Leverage Staking Are Shaping DeFi’s Risk Landscape
3 Background
4 System Model and 4.1 System Participants
4.2 Leverage Staking with LSDs
7.1 stETH Price Deviation and Terra Crash
7.2 Cascading Liquidation and User Behaviors
8 Stress Testing
8.1 Motivation and 8.2 Simulation
9 Discussion and Future Research Directions
A. Aave Parameter Configuration
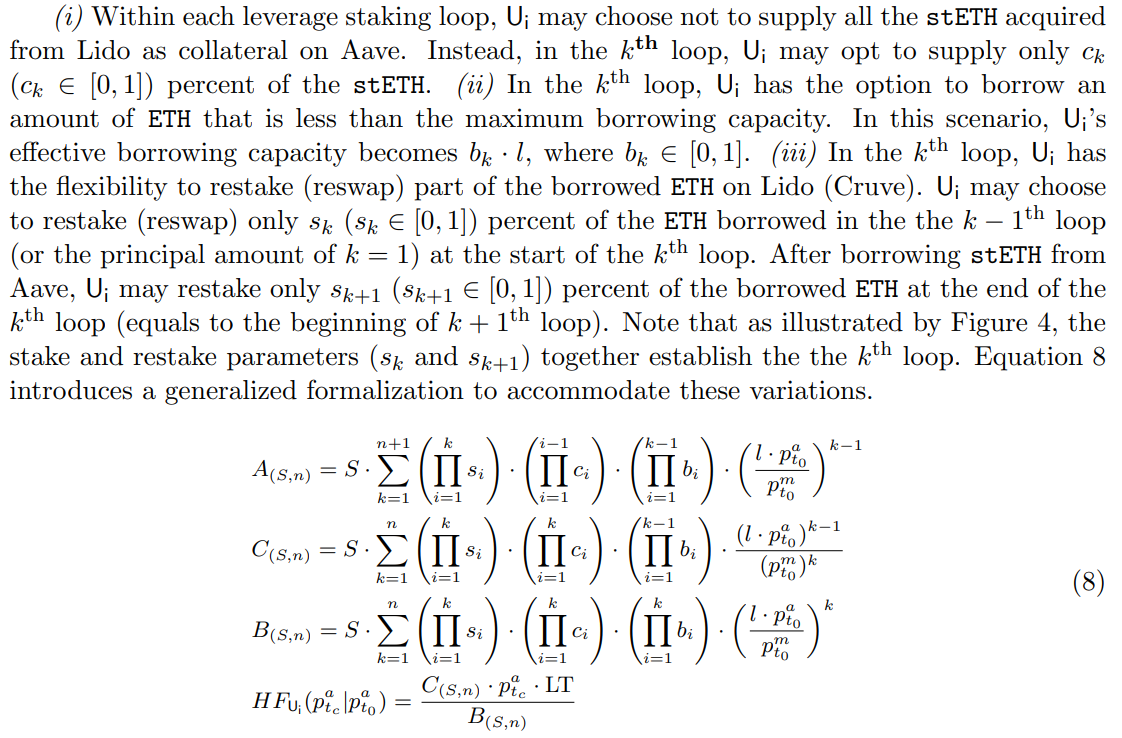
B. Generalized Formalization For Leverage Staking
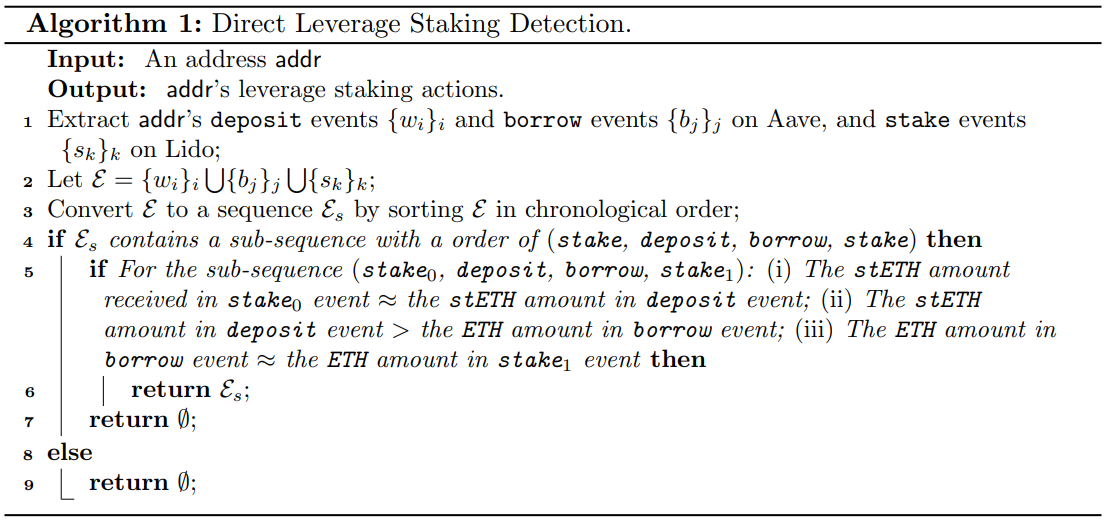
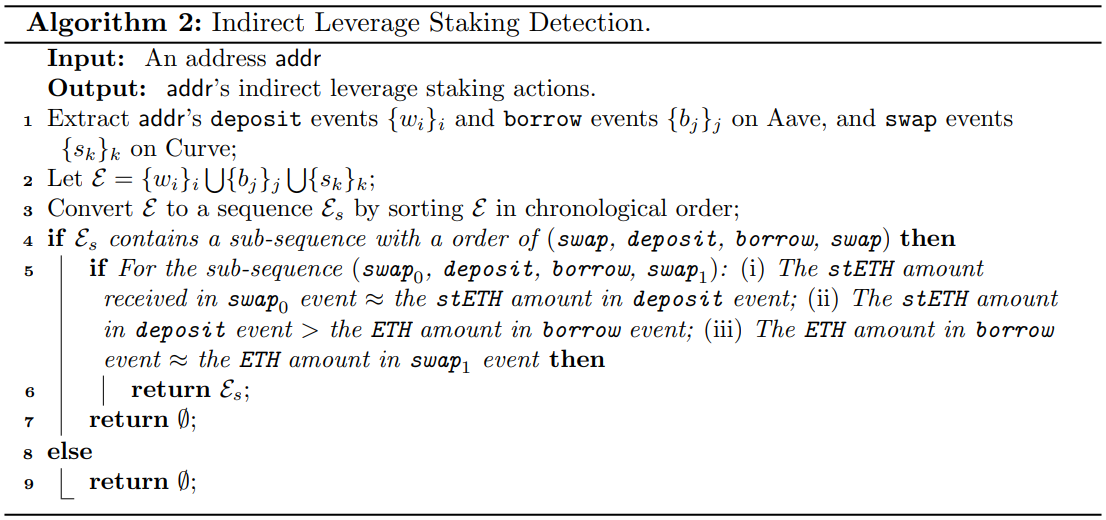
C. Leverage Staking Detection Algorithm
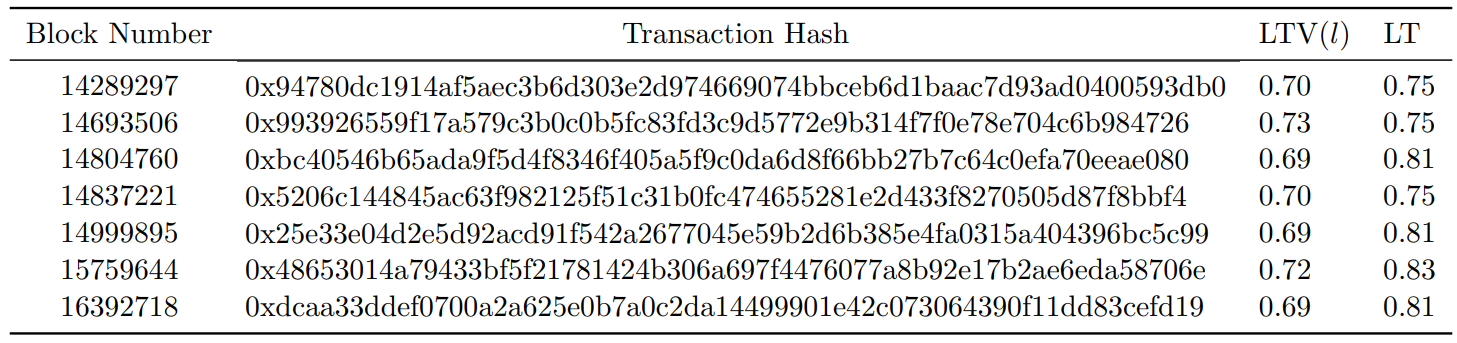
A Aave Parameter ConfigurationTable 3 depicts the historical changes of Aave parameter configurations. We crawl the collateralConfigurationChanged events for Aave V2 lending pool.
In addition to the standardized cases discussed in Section 5, real-world leverage lending situations can exhibit substantial variation among users. Specifically, we delineate the following variations using the direct leverage staking strategy as an example.
\
\
Algorithms 1 and 2 depict the heuristics used to detect addresses that have performed direct and indirect leverage staking respectively.
\
\
\
\
\
\
:::info Authors:
(1) Xihan Xiong, Imperial College London, UK;
(2) Zhipeng Wang, Imperial College London, UK;
(3) Xi Chen, University of Sussex, UK;
(4) William Knottenbelt, Imperial College London, UK;
(5) Michael Huth, Imperial College London, UK.
:::
:::info This paper is available on arxiv under CC BY 4.0 DEED license.
:::
\
- Home
- About Us
- Write For Us / Submit Content
- Advertising And Affiliates
- Feeds And Syndication
- Contact Us
- Login
- Privacy
All Rights Reserved. Copyright , Central Coast Communications, Inc.